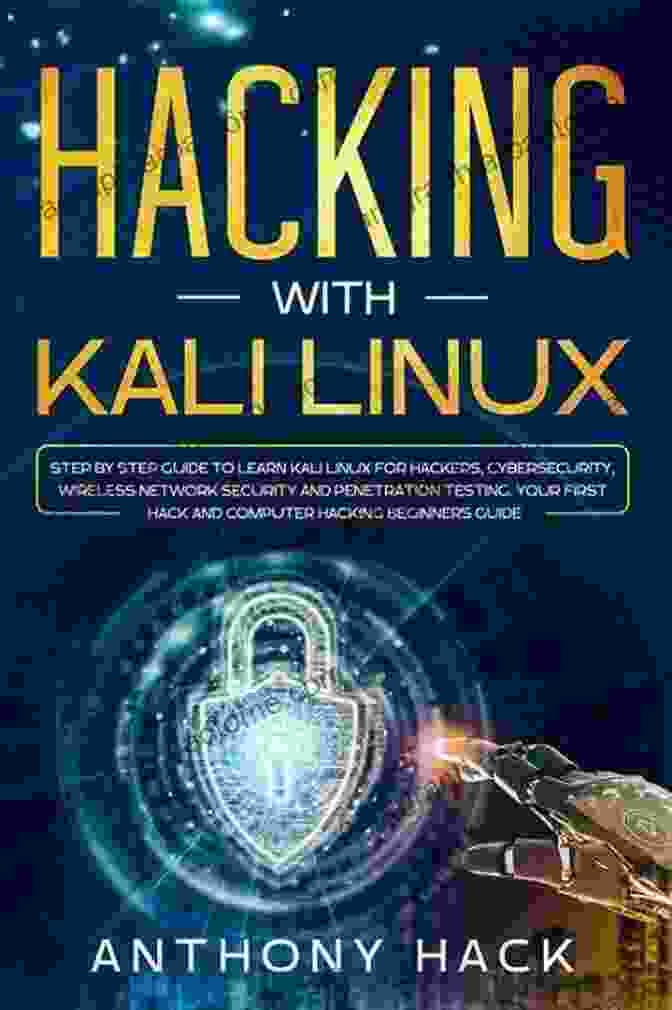
Master Cybersecurity: Network Hacking and Penetration Testing with the Power of Linux

In today's digital age, cybersecurity has become paramount for protecting sensitive information and safeguarding networks. While understanding the fundamentals of cybersecurity is crucial, gaining practical experience in network hacking and penetration testing is the key to staying one step ahead of potential threats.
If you're aspiring to become a cybersecurity expert, there's no better tool than Linux. This open-source operating system empowers you with a vast array of powerful tools and techniques to enhance your cybersecurity skills.
5 out of 5
| Language | : | English |
| File size | : | 1076 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 238 pages |
| Lending | : | Enabled |
To help you embark on this exciting journey, our team of acclaimed cybersecurity experts has crafted a comprehensive book: Learn Cybersecurity Network Hacking And Penetration Testing With The Best Linux.
Unleash the Power of Linux for Ethical Hacking
In this book, you'll delve into the fundamentals of Linux, exploring its powerful command line and diverse toolset. You'll learn how to navigate the Linux environment, manage files, and utilize essential commands.
As you progress through the book, you'll master the art of network hacking and penetration testing. We'll guide you through various techniques to discover vulnerabilities, exploit weaknesses, and gain unauthorized access to systems.
Real-World Scenarios and In-Depth Analysis
To ensure you're equipped with practical knowledge, our book presents real-world scenarios and detailed step-by-step instructions. You'll learn how to:
- Configure and use Kali Linux, the premier tool for ethical hacking
- Perform reconnaissance and information gathering techniques
- Identify and exploit vulnerabilities in networks and systems
- Utilize advanced tools for password cracking, vulnerability scanning, and exploitation
- Safely and ethically conduct penetration tests
Our book not only teaches you the techniques but also provides a deep understanding of the underlying principles and concepts. This knowledge will empower you to adapt to evolving security threats and stay abreast of the latest industry best practices.
Benefits of This Essential Cybersecurity Book
By investing in our book, you'll gain:
- A comprehensive understanding of Linux as a cybersecurity platform
- Practical experience in network hacking and penetration testing
- Real-world examples and in-depth analysis
- A foundation for advanced cybersecurity training and certifications
- Insights from experienced cybersecurity practitioners
Target Audience
Our book is designed for:
- Aspiring cybersecurity professionals
- Network administrators seeking to enhance their security skills
- Ethical hackers interested in honing their craft
- Students pursuing cybersecurity degrees or certifications
- Anyone seeking a deep understanding of network hacking and penetration testing
About the Authors
Our team of authors consists of experienced cybersecurity experts with years of industry experience. They have conducted countless penetration tests, discovered numerous vulnerabilities, and helped organizations protect their networks from malicious actors.
Their passion for cybersecurity is evident in their meticulous research and engaging writing style. They have poured their knowledge and expertise into this book to empower you with the skills and knowledge you need to excel in the field of cybersecurity.
Call to Action
Don't let this opportunity to enhance your cybersecurity skills pass you by. Free Download your copy of Learn Cybersecurity Network Hacking And Penetration Testing With The Best Linux today and embark on a journey to master network hacking and penetration testing.
With our book as your guide, you'll not only expand your cybersecurity knowledge but also gain the practical experience necessary to protect networks, detect vulnerabilities, and stay ahead of cyber threats.
Invest in your future and unlock the power of Linux for ethical hacking and penetration testing. Free Download your copy now and let the journey begin!
5 out of 5
| Language | : | English |
| File size | : | 1076 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 238 pages |
| Lending | : | Enabled |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia John Ayto
John Ayto Amanda Lamb
Amanda Lamb Jessica Milner Davis
Jessica Milner Davis Richard E Grant
Richard E Grant Whiskey Ranch Horse
Whiskey Ranch Horse Mattie Nottage
Mattie Nottage Jenny Pearson
Jenny Pearson Jim Anderson
Jim Anderson Victoria Rosenthal
Victoria Rosenthal Joanna Albrecht
Joanna Albrecht Kim Campbell
Kim Campbell John Keaton
John Keaton Shawn Coyne
Shawn Coyne John Lex Robinson
John Lex Robinson Steve Agren
Steve Agren Jhenah Telyndru
Jhenah Telyndru Jisun Sunny Fisher
Jisun Sunny Fisher Jim Garton
Jim Garton Nathan Rabin
Nathan Rabin Lars Brownworth
Lars Brownworth
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Dwayne MitchellTales of the Lehigh Valley Timing Association: Wally Ely's Personal Short...
Dwayne MitchellTales of the Lehigh Valley Timing Association: Wally Ely's Personal Short... Tennessee WilliamsFollow ·8.4k
Tennessee WilliamsFollow ·8.4k Eric HayesFollow ·16.8k
Eric HayesFollow ·16.8k Arthur Conan DoyleFollow ·15.1k
Arthur Conan DoyleFollow ·15.1k Duncan CoxFollow ·15.7k
Duncan CoxFollow ·15.7k Tom ClancyFollow ·7.9k
Tom ClancyFollow ·7.9k Branson CarterFollow ·5.4k
Branson CarterFollow ·5.4k Eli BlairFollow ·15.8k
Eli BlairFollow ·15.8k Frank ButlerFollow ·10.1k
Frank ButlerFollow ·10.1k
 Julio Cortázar
Julio CortázarAn Illustrated Encyclopedia Of Live Concerts And...
Immerse yourself in the...
 Edgar Cox
Edgar CoxNon Physically Assaultive Attachment Based Chronic Covert...
What is Covert...
 Robert Reed
Robert ReedThe Baseball of Why: Unraveling the Intricacies of...
Step up to the plate and...
 Aldous Huxley
Aldous HuxleyTacos and Beer: An Atmosphere of Flavorful Delights
In the realm of culinary adventures,...
 Stan Ward
Stan WardUnlock the Secrets of the Aramaic Jesus: Revelations of a...
Journey Back to the Roots of...
 Vincent Mitchell
Vincent MitchellMillionaire Success Strategies: Your Blueprint for...
Unlock the...
5 out of 5
| Language | : | English |
| File size | : | 1076 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 238 pages |
| Lending | : | Enabled |